We offer end-to-end cybersecurity consulting services designed to build a wall around your digital assets. From 24/7 monitoring to regulatory compliance, we ensure your organization is resilient against modern cyber threats.

Continuous protection without the overhead. Our Security Operations Center (SOC) provides continuous monitoring of your network, using AI-driven threat intelligence to detect and neutralize anomalies before they become breaches.

Secure cloud adoption without blind spots. We design and implement Zero Trust architectures for AWS, Azure, and Google Cloud, ensuring your cloud workloads are protected by strict identity management and encryption protocols.
Navigate regulations with ease. Our cybersecurity services help you achieve and maintain compliance with global standards like GDPR, HIPAA, SOC 2, and ISO 27001, streamlining audits and reducing legal liability.

Secure every device. Similar to other top cyber security companies, we deploy advanced EDR agents on laptops, servers, and mobile devices to block malware, ransomware, and file-less attacks at the entry point.
Expert help when you need it most. In the event of a breach, our rapid response team jumps in to contain the threat, recover data, and conduct forensic analysis to prevent recurrence.
We offer end-to-end cybersecurity consulting services designed to build a wall around your digital assets. From 24/7 monitoring to regulatory compliance, we ensure your organization is resilient against modern cyber threats.

Continuous protection without the overhead. Our Security Operations Center (SOC) provides continuous monitoring of your network, using AI-driven threat intelligence to detect and neutralize anomalies before they become breaches.

Secure cloud adoption without blind spots. We design and implement Zero Trust architectures for AWS, Azure, and Google Cloud, ensuring your cloud workloads are protected by strict identity management and encryption protocols.

Navigate regulations with ease. Our cybersecurity services help you achieve and maintain compliance with global standards like GDPR, HIPAA, SOC 2, and ISO 27001, streamlining audits and reducing legal liability.

Secure every device. Similar to other top cyber security companies, we deploy advanced EDR agents on laptops, servers, and mobile devices to block malware, ransomware, and file-less attacks at the entry point.

Expert help when you need it most. In the event of a breach, our rapid response team jumps in to contain the threat, recover data, and conduct forensic analysis to prevent recurrence.
Quality is engineered into every stage of our development process. Our approach combines intelligent automation, real-world testing environments, and seamless pipeline integration to ensure consistent, release-ready performance.
We operate on the principle of "never trust, always verify." Every user, device, and connection is authenticated continuously, minimizing the blast radius of any potential intrusion.
We don't just wait for alarms to ring. Our analysts actively search your network for hidden threats and dormant malware that automated tools might miss.
We integrate with your existing tech stack. Whether you use Splunk, CrowdStrike, or Microsoft Sentinel, we optimize your current tools rather than forcing a "rip and replace.
Security shouldn't slow you down. We design security controls that enable safe business operations without creating unnecessary friction for your employees.
We can deploy sensors and agents across your infrastructure in hours, not weeks, providing immediate visibility into your security posture.
See how we’ve helped organizations prevent breaches, reduce audit failures, and maintain business continuity through proactive IT security solutions.
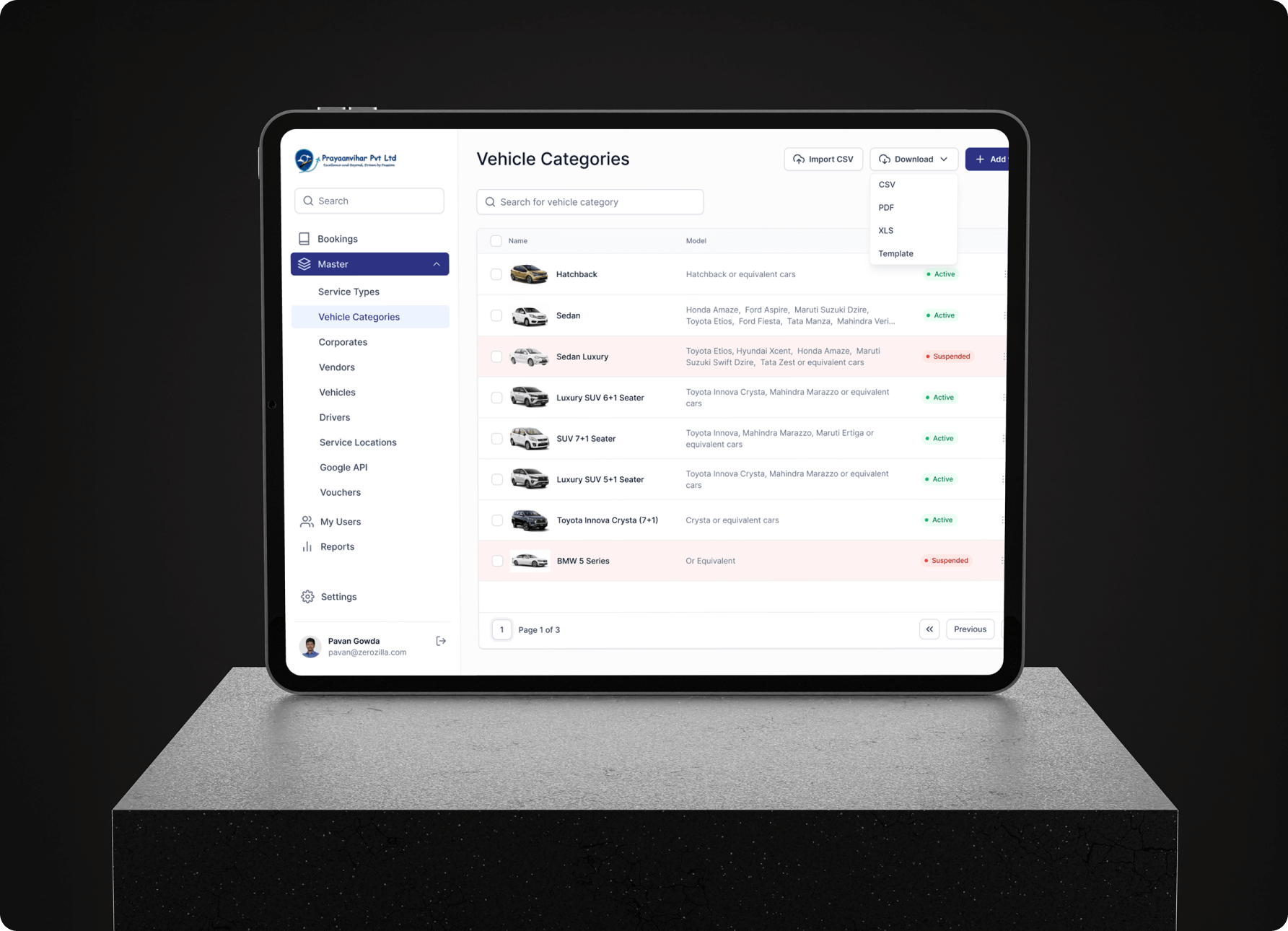
From 10-minute manual bookings to 60-second automated workflows, discover how we helped a corporate travel desk eliminate spreadsheet chaos, slash booking errors, and achieve 2× user growth.
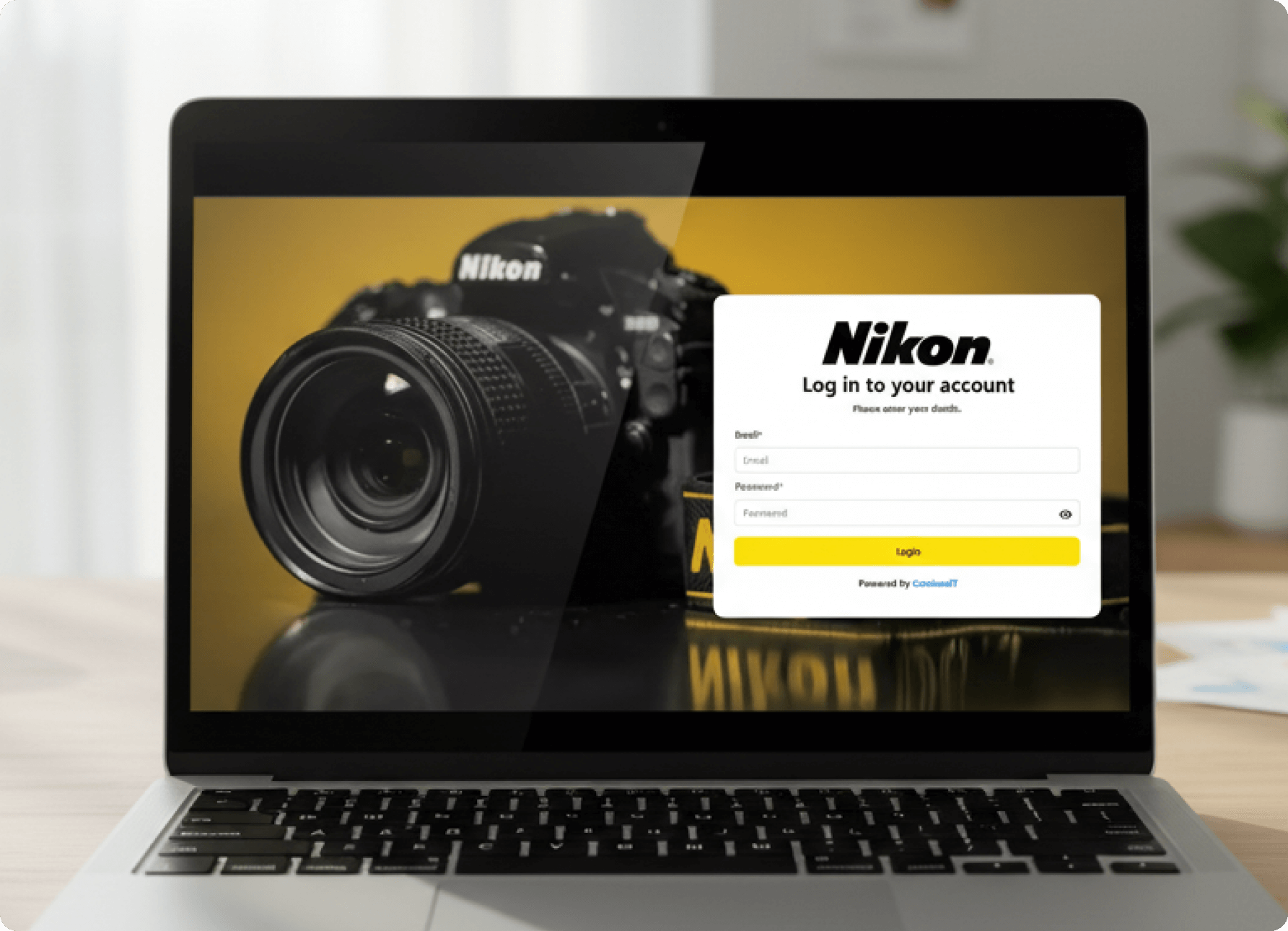
Complete operational control in one platform. 60% faster processing, claims resolved in hours, zero spreadsheet chaos. See how we unified fragmented systems with scalable infrastructure for a major optics manufacturer.
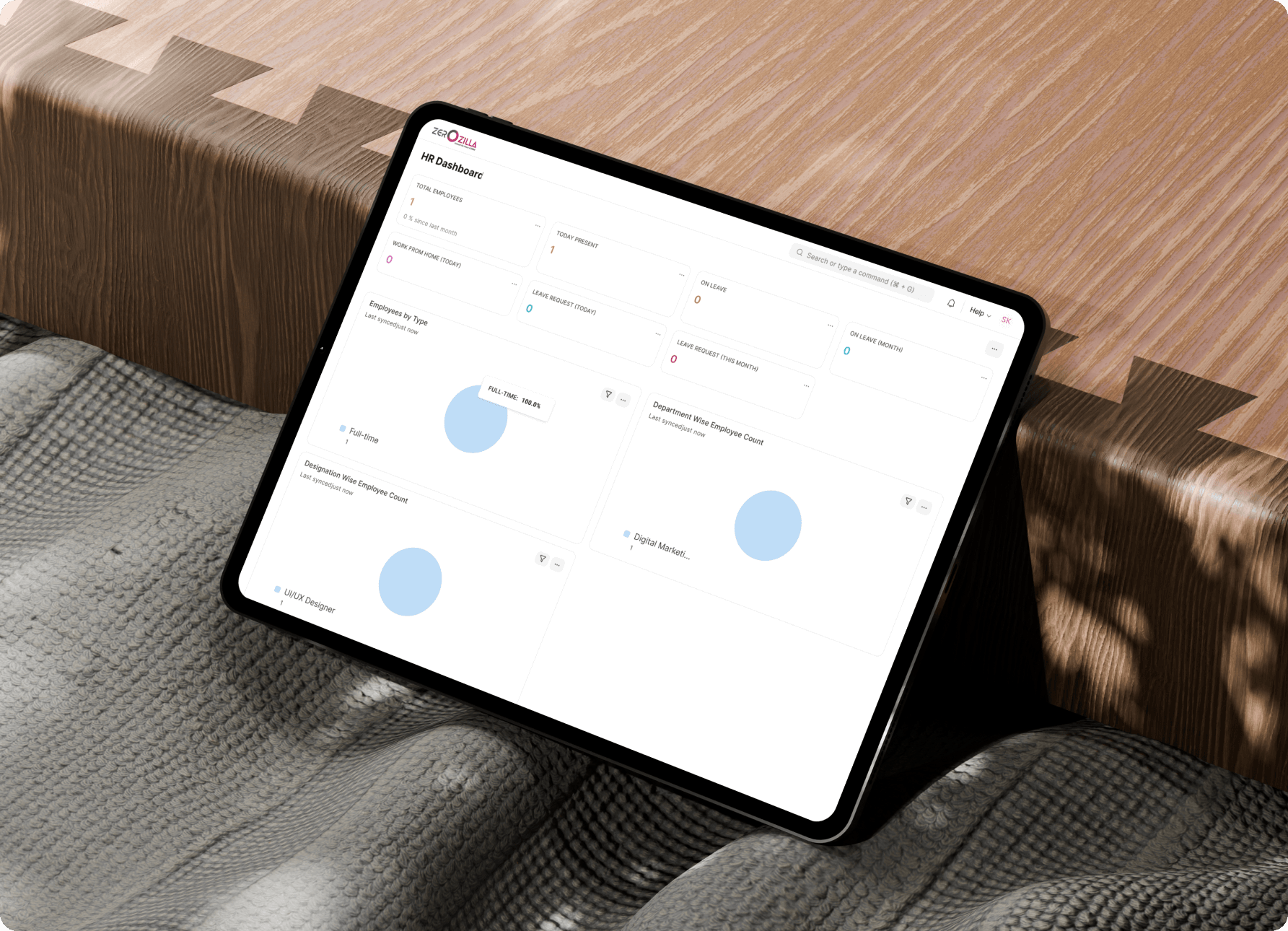
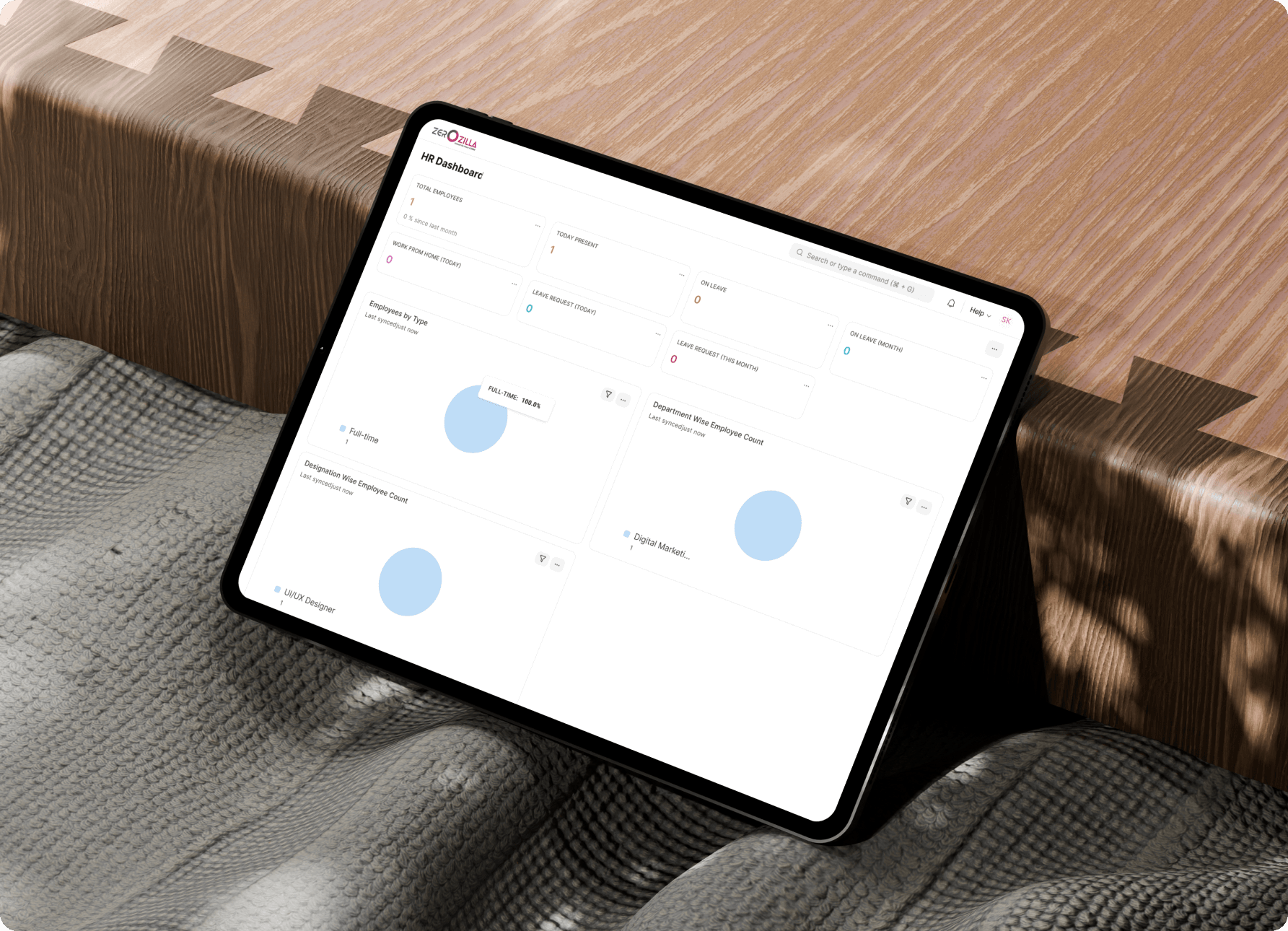
Automated HR workflows. Real-time insights. Self-service employee tools. Zero spreadsheet chaos. See how we transformed fragmented HR operations into a unified, compliance-ready system.
Complete operational control in one platform. 60% faster processing, claims resolved in hours, zero spreadsheet chaos. See how we unified fragmented systems with scalable infrastructure for a major optics manufacturer.
Automated HR workflows. Real-time insights. Self-service employee tools. Zero spreadsheet chaos. See how we transformed fragmented HR operations into a unified, compliance-ready system.
Our team holds top-tier certifications (CISSP, CISM, CEH, OSCP), ensuring your security is managed by the most qualified hands in the industry.
Building an internal SOC is expensive. We provide enterprise-grade security capabilities at a fraction of the cost of hiring a full in-house team.
We don't view security in isolation. We work with your developers and operations teams (DevSecOps) to bake security into your products from day one.

As an emerging business, Gateway sought a comprehensive solution to bolster our website, graphic design endeavors, and IT requirements. Zerozilla came highly recommended, and rightfully so. They epitomize reliability, ease of collaboration, affordability, and consistently deliver outstanding results. Without a doubt, Zerozilla is an invaluable partner for Gateway International Group, and we extend our sincere gratitude.

We have used the services of Zerozilla for building our website. The team led by Thunga and Vinay is quite responsive, flexible, creative, and methodical. They have been able to add significant value by overhauling our website and bringing it a contemporary look. The inputs particularly on improving the SEO are well appreciated.

A special thanks to our external development partner, Zerozilla, for their exceptional work in helping us go live with an upgraded landing and details page. The feature, which displays real-time return statuses, has already received glowing feedback. Zerozilla exceeded our expectations by delivering ahead of schedule with impeccable quality. This achievement highlights the power of strong partnerships and collaboration. Thank you, Zerozilla, for your stellar contribution!
Working with Zerozilla has been an absolute pleasure! Their expertise in website development truly shone through as they helped us completely revamp our online presence. The team at Zerozilla displayed a remarkable level of innovation. Communication was seamless throughout the process. The Zerozilla team’s professionalism was exemplary. Thanks to their dedication and expertise, we now have a website that reflects our work and provides visitors with a fresh perspective and an exceptional user experience.
We’ve found that the best software comes from the best partnerships. Here’s how we work with you as a trusted software development company
We perform a gap analysis of your current defenses against NIST or ISO frameworks.
We create a security roadmap tailored to your risk profile and business goals.
We configure firewalls, patch vulnerabilities, and deploy protection agents.
Our SOC begins 24/7 surveillance of your logs and traffic.
When a threat is detected, automated playbooks and human analysts neutralize it instantly.
We provide executive dashboards and update your defenses based on the latest global threat intelligence.
We’ve found that the best software comes from the best partnerships. Here’s how we work with you as a trusted software development company
We perform a gap analysis of your current defenses against NIST or ISO frameworks.
We create a security roadmap tailored to your risk profile and business goals.
We configure firewalls, patch vulnerabilities, and deploy protection agents.
Our SOC begins 24/7 surveillance of your logs and traffic.
When a threat is detected, automated playbooks and human analysts neutralize it instantly.
We provide executive dashboards and update your defenses based on the latest global threat intelligence.
Find quick answers to common questions about our cyber security services and delivery process
We discuss your concerns and compliance needs.
We scan your perimeter to find open doors.
We present a plan to close gaps and secure your network.
WhatsApp us
Hear from our clients and why 200 + businesses trust Zerozilla.
As an emerging business, Gateway sought a comprehensive solution to bolster our website, graphic design endeavors, and IT requirements. Zerozilla came highly recommended, and rightfully so. They epitomize reliability, ease of collaboration, affordability, and consistently deliver outstanding results. Without a doubt, Zerozilla is an invaluable partner for Gateway International Group, and we extend our sincere gratitude.

A special thanks to our external development partner, Zerozilla, for their
exceptional work in helping us go live with an upgraded landing and details page. The feature, which displays real-time return statuses, has already received glowing feedback. Zerozilla exceeded our expectations by delivering ahead of schedule with impeccable quality. This achievement highlights the power of strong partnerships and collaboration. Thank you, Zerozilla, for your stellar contribution!